What is Cyber Security?

Hello everyone!!!
In this article, I like to tell you about the importance of cybersecurity. After reading this article, you will get a proper idea about Cyber Security.
Computer security focuses on protecting information, hardware, and software from unauthorized use as well as preventing damage from intrusions, sabotage, and natural disasters. Someone who gains unauthorized access to computers that contain information about us is commonly known as a computer hacker. Not all hackers are intent on malicious actions and not all are criminals.
Cybersecurity is the practice of defending computers, servers, mobile devices, electronic systems, networks, and data from malicious attacks. It’s also known as information technology security or electronic information security. The term applies in a variety of contexts, from business to mobile computing, and can be divided into a few common categories.
· Network security is the practice of securing a computer network from intruders, whether targeted attackers or opportunistic malware.
· Application security focuses on keeping software and devices free of threats. A compromised application could provide access to the data its designed to protect. Successful security begins in the design stage, well before a program or device is deployed.
· Information security protects the integrity and privacy of data, both in storage and in transit.
· Operational security includes the processes and decisions for handling and protecting data assets. The permissions users have when accessing a network and the procedures that determine how and where data may be stored or shared all fall under this umbrella.
· Disaster recovery and business continuity define how an organization responds to a cyber-security incident or any other event that causes the loss of operations or data. Disaster recovery policies dictate how the organization restores its operations and information to return to the same operating capacity as before the event. Business continuity is the plan the organization falls back on while trying to operate without certain resources.
· End-user education addresses the most unpredictable cyber-security factor: people. Anyone can accidentally introduce a virus to an otherwise secure system by failing to follow good security practices. Teaching users to delete suspicious email attachments, not plug in unidentified USB drives, and various other important lessons is vital for the security of any organization.
Types of cyber threats
The threats countered by cyber-security are three-fold:
1. Cybercrime includes single actors or groups targeting systems for financial gain or to cause disruption.
2. Cyber-attack often involves politically motivated information gathering.
3. Cyberterrorism is intended to undermine electronic systems to cause panic or fear.
So, how do malicious actors gain control of computer systems? Here are some common methods used to threaten cyber-security:
Malware
Malware means malicious software. One of the most common cyber threats, malware is software that a cybercriminal or hacker has created to disrupt or damage a legitimate user’s computer. Often spread via an unsolicited email attachment or legitimate-looking download, malware may be used by cybercriminals to make money or in politically motivated cyber-attacks.

There are several different types of malware, including:
· Virus: A self-replicating program that attaches itself to clean file and spreads throughout a computer system, infecting files with malicious code.
· Trojans: A type of malware that is disguised as legitimate software. Cybercriminals trick users into uploading Trojans onto their computer where they cause damage or collect data.
· Spyware: A program that secretly records what a user does, so that cybercriminals can make use of this information. For example, spyware could capture credit card details.
· Ransomware: Malware which locks down a user’s files and data, with the threat of erasing it unless a ransom is paid.
· Adware: Advertising software that can be used to spread malware.
· Botnets: Networks of malware-infected computers which cybercriminals use to perform tasks online without the user’s permission.
SQL injection

An SQL (structured language query) injection is a type of cyber-attack used to take control of and steal data from a database. Cybercriminals exploit vulnerabilities in data-driven applications to insert malicious code into a database via a malicious SQL statement. This gives them access to the sensitive information contained in the database.
Phishing

Phishing is when cybercriminals target victims with emails that appear to be from a legitimate company asking for sensitive information. Phishing attacks are often used to dupe people into handing over credit card data and other personal information.
Man-in-the-middle attack
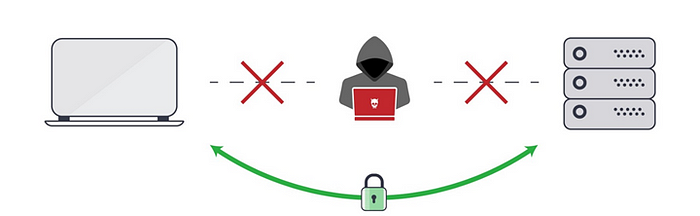
A man-in-the-middle attack is a type of cyber threat where a cybercriminal intercepts communication between two individuals in order to steal data. For example, on an unsecured WiFi network, an attacker could intercept data being passed from the victim’s device and the network.
Denial-of-service attack

A denial-of-service attack is where cybercriminals prevent a computer system from fulfilling legitimate requests by overwhelming the networks and servers with traffic. This renders the system unusable, preventing an organization from carrying out vital functions.
The CIA triad

Confidentiality, integrity, and availability, also known as the CIA triad, is a model designed to guide policies for information security within an organization. Elements of the triad are three of the most foundational and crucial cybersecurity needs, experts believe the CIA triad needs an upgrade to stay effective.
The following is a breakdown of the three key concepts that form the CIA triad:
· Confidentiality is roughly equivalent to Confidentiality measures are designed to prevent sensitive information from unauthorized access attempts. It is common for data to be categorized according to the amount and type of damage that could be done if it fell into the wrong hands. More or less stringent measures can then be implemented according to those categories.
· Integrity involves maintaining the consistency, accuracy, and trustworthiness of data over its entire lifecycle. Data must not be changed in transit, and steps must be taken to ensure data cannot be altered by unauthorized people (for example, in a breach of confidentiality).
· Availability means information should be consistently and readily accessible for authorized parties. This involves properly maintaining hardware and technical infrastructure and systems that hold and display the information.
Why the CIA triad is important
With each letter representing a foundational principle in cybersecurity, the importance of the CIA triad security model speaks for itself. Confidentiality, integrity, and availability together are considered the three most important concepts within information security.
Considering these three principles together within the framework of the “triad” can help guide the development of security policies for organizations. When evaluating needs and use cases for potential new products and technologies, the triad helps organizations ask focused questions about how value is being provided in those three key areas.
Thinking of the CIA triad’s three concepts together as an interconnected system, rather than as independent concepts, can help organizations understand the relationships between the three.
Here are examples of the various management practices and technologies that comprise the CIA triad.
Confidentiality
Sometimes safeguarding data confidentiality involves special training for those privies to sensitive documents. Training can help familiarize authorized people with risk factors and how to guard against them. Further aspects of training may include strong passwords and password-related best practices and information about social engineering methods to prevent users from bending data-handling rules with good intentions and potentially disastrous results.
A good example of methods used to ensure confidentiality is requiring an account number or routing number when banking online. Data encryption is another common method of ensuring confidentiality. User IDs and passwords constitute a standard procedure; two-factor authentication (2FA) is becoming the norm. Other options include biometric verification and security tokens, key fobs, or soft tokens. In addition, users can take precautions to minimize the number of places where information appears and the number of times it is actually transmitted to complete a required transaction. Extra measures might be taken in the case of extremely sensitive documents, such as storing only on air-gapped computers, disconnected storage devices, or, for highly sensitive information, in hard-copy form.
Integrity
These measures include file permissions and user access controls. Version control may be used to prevent erroneous changes or accidental deletion by authorized users from becoming a problem. In addition, organizations must put in some means to detect any changes in data that might occur as a result of non-human-caused events such as an electromagnetic pulse (EMP) or server crash.
Data might include checksums, even cryptographic checksums, for verification of integrity. Backups or redundancies must be available to restore the affected data to its correct state. Furthermore, digital signatures can be used to provide effective nonrepudiation measures, meaning evidence of logins, messages sent, electronic document viewing, and sending cannot be denied.
Availability
This is best ensured by rigorously maintaining all hardware, performing hardware repairs immediately when needed, and maintaining a properly functioning operating system (OS) environment that is free of software conflicts. It’s also important to keep current with all necessary system upgrades. Providing adequate communication bandwidth and preventing the occurrence of bottlenecks are equally important tactics. Redundancy, failover, RAID even high-availability clusters can mitigate serious consequences when hardware issues do occur.
Fast and adaptive disaster recovery is essential for the worst-case scenarios; that capacity relies on the existence of a comprehensive DR plan. Safeguards against data loss or interruptions in connections must include unpredictable events such as natural disasters and fire. To prevent data loss from such occurrences, a backup copy may be stored in a geographically isolated location, perhaps even in a fireproof, waterproof safe. Extra security equipment or software such as firewalls and proxy servers can guard against downtime and unreachable data blocked by malicious denial-of-service (DoS) attacks and network intrusions.
End-user protection

End-user protection or endpoint security is a crucial aspect of cybersecurity. After all, it is often an individual (the end-user) who accidentally uploads malware or another form of cyber threat to their desktop, laptop, or mobile device.
So, how do cyber-security measures protect end-users and systems? First, cyber-security relies on cryptographic protocols to encrypt emails, files, and other critical data. This not only protects information in transit but also guards against loss or theft.
In addition, end-user security software scans computers for pieces of malicious code, quarantines this code, and then removes it from the machine. Security programs can even detect and remove malicious code hidden in primary boot records and are designed to encrypt or wipe data from a computer’s hard drive.
Electronic security protocols also focus on real-time malware detection. Many use heuristic and behavioral analysis to monitor the behavior of a program and its code to defend against viruses or Trojans that change their shape with each execution. Security programs can confine potentially malicious programs to a virtual bubble separate from a user’s network to analyze their behavior and learn how to better detect new infections.
Security programs continue to evolve new defenses as cyber-security professionals identify new threats and new ways to combat them. To make the most of end-user security software, employees need to be educated about how to use it. Crucially, keeping it running and updating it frequently ensures that it can protect users against the latest cyber threats.
Cyber safety tips — protect yourself against cyberattacks
How can businesses and individuals guard against cyber threats? Here are our top cyber safety tips:
1. Update your software and operating system: This means you benefit from the latest security patches.
2. Use anti-virus software: Security solutions like Kaspersky Total Security will detect and removes threats. Keep your software updated for the best level of protection.
3. Use strong passwords: Ensure your passwords are not easily guessable.
4. Do not open email attachments from unknown senders: These could be infected with malware.
5. Do not click on links in emails from unknown senders or unfamiliar websites: This is a common way that malware is spread.
6. Avoid using unsecured Wi-Fi networks in public places: Unsecure networks leave you vulnerable to man-in-the-middle attacks.
Thank you very much for reading!
Hope to see you again with another article. Till then, Goodbye All!
